1.9 Data Communication
Data Communication refers to the process of exchanging data or information between two or more devices or systems through a transmission medium such as cables, optical fibers, or wireless mediums. This communication can involve the transfer of various types of data, including text, numbers, images, audio, and video. It is a fundamental component of modern information technology and telecommunications.
Network Communication Components
Network communication consists of five basic components:
- Sender: Also known as the transmitter, it is a computer or device that sends the message (data or information) from the source to the destination in a communication network. It may be a computer, workstation, cell phone, or camera.
- Message: The data or information to be transmitted, which can be in the form of text, audio, video, or any combination of these.
- Medium: The path through which the message travels from source to destination. It can be wired (e.g., telephone cable, coaxial cable, fiber optics) or wireless (e.g., Bluetooth, Wi-Fi, microwave, radio wave, satellite).
- Receiver: The device that receives the transmitted message. It can be a computer, workstation, telephone handset, or television set.
- Protocol: A set of rules that governs data communications. It represents an agreement between the communicating devices, ensuring they can communicate effectively.
Modes of Network Communication
Modes of network communication refer to the methods or ways information is transmitted from one place to another. The following are different modes of data communication:
- Simplex Mode: Allows communication in only one direction. The receiver cannot send data back to the sender. Examples include electronic notice boards, radio, and television broadcasting.
- Half-Duplex Mode: Allows communication in both directions, but not at the same time. The sender and receiver take turns sending and receiving data. An example is a walkie-talkie, where each party must indicate when they have finished speaking.
- Full-Duplex Mode: Allows communication in both directions simultaneously. Both sender and receiver can send and receive data at the same time. Examples include telephone networks, where both parties can talk and listen simultaneously.
- Asynchronous Transmission: Involves variable time intervals between two characters. It uses start and stop bits for synchronization. This type is ideal for slow-speed communication where gaps may occur, such as keyboard data transmission.
- Synchronous Transmission: Has fixed time intervals between characters. The sender and receiver are synchronized, sending data as a continuous stream without start and stop bits. It is faster than asynchronous transmission due to fewer control bits and is used in network communication links.
Communication Devices
A Communication Device is used in telecommunication systems to transmit data from one location to another. Commonly used devices include:
- Hub: A connectivity device used in LAN. It connects multiple LAN devices on one network, making them act as a single network. It is non-intelligent and sends output to all devices on the network.
- Switch: Performs the same job as a hub but is more intelligent. It forwards data packets only to the intended recipient node, using information about the data packet.
- Router: Connects two or more networks, forwarding data packets by selecting the best pathway based on network traffic. It connects local networks to the internet and routes data efficiently.
- Gateway: Connects different networks that use different protocols. It changes the format of data packets without altering the message content to make them conform to the application program of the remote computer.
Network Architecture
Network Architecture is the design of a communication system, including hardware devices, cabling, network topology, and connections. It consists of server computers and client computers.
Client/Server Networks
Client/Server Network is a network where computers act as either servers or clients. Servers provide resources like information, software, printers, and internet connections. Clients access these shared resources. This architecture centralizes control of data, enhancing security and management.
Peer-to-Peer Networks
Peer-to-Peer Network allows every computer to act as both client and server. Each computer can share files and access shared resources, making it flexible but difficult to manage as it grows larger.
Types of Networks
Different types of networks exist based on the size and area they cover:
Local Area Networks (LAN)
Wide Area Networks (WAN)
Metropolitan Area Network (MAN)
Virtual Private Network (VPN)
Wireless Networks
Wireless Networks use wireless communication technologies to transmit data between devices without physical wired connections. They can operate over short distances (e.g., within a building) or large geographical areas (e.g., cellular networks).
Examples of Wireless Networks
- Wi-Fi (Wireless Fidelity): Connects devices to local area networks and the internet wirelessly. Common in homes, offices, and public places.
- Bluetooth: Short-range wireless technology for connecting devices like headsets, keyboards, and mice.
- Cellular Networks: Provide wireless communication over large areas, enabling mobile voice calls, messaging, and internet access.
- Satellite Networks: Use satellites for wireless connectivity over large areas, used for internet access, TV broadcasting, and GPS.
Advantages of Wireless Networks
- Mobility: Allows users to access the internet and network resources from anywhere within the coverage area.
- Cost-effective: Easier and cheaper to install without the need for cables.
- Scalability: Easily expands to accommodate additional devices and users.
- Flexibility: Supports multiple devices for communication and data sharing.
- Remote Access: Facilitates remote access to network resources, enabling work from home or on the go.
Disadvantages of Wireless Networks
- Interference: Affected by interference from other devices and environmental factors.
- Security Risks: Vulnerable to unauthorized access and data breaches.
- Limited Range: Requires boosters for extended coverage.
- Performance: Can be slower in busy environments.
- Reliability: Issues with dropped signals and slow connections.
- Power Consumption: Wireless devices consume more power than wired devices.
Network Topologies
Network Topology refers to the arrangement of network nodes and connections between them. It represents the layout of nodes and connections in the network.
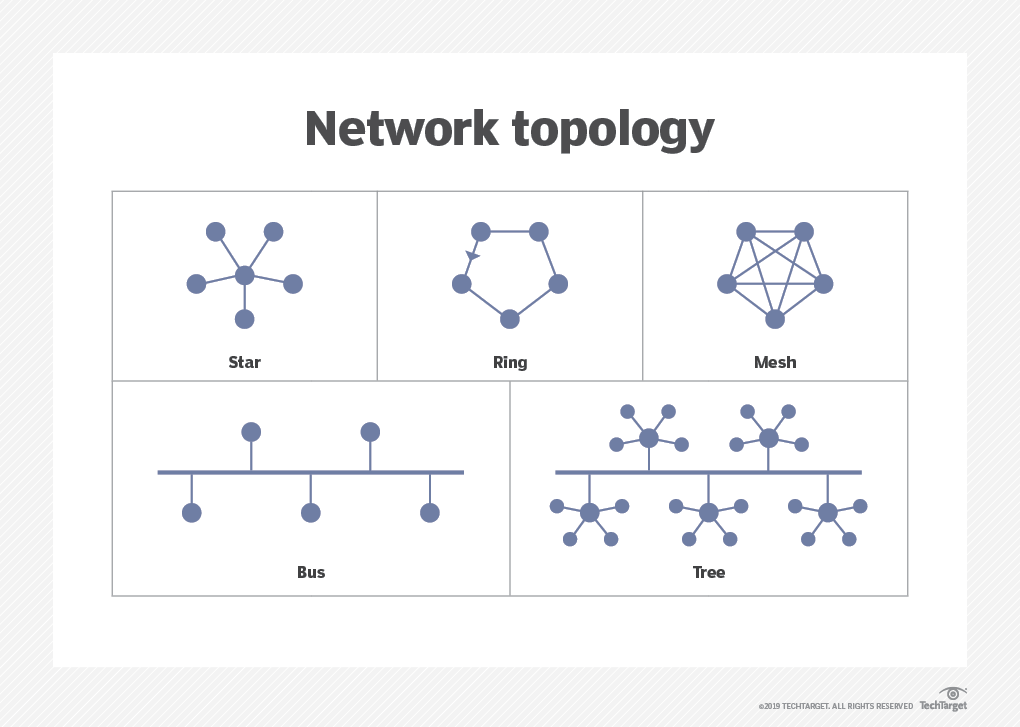
Bus Topology
Bus Topology connects each node along a single piece of cable called a bus. Signals are sent to all devices, and terminators are used to prevent signal reflection.
Features of Bus Topology:
- Simple: Suitable for small networks.
- Easy Connection: Easy to connect devices.
- Cost-effective: Requires less cable.
Limitations of Bus Topology:
- Single Point of Failure: Cable damage affects the entire network.
- Troubleshooting: Difficult to identify problems.
- Scalability: Not suitable for large networks.
Star Topology
Star Topology connects each node to a central device called a hub. Hubs can be connected to create larger networks.
Features of Star Topology:
- Scalability: Suitable for both small and large networks.
- Fault Detection: Easy to detect and remove faults.
- Reliability: Cable failure does not affect the entire network.
Limitations of Star Topology:
- Hub Failure: Hub failure affects the entire network.
- Cost: Expensive to implement with lengthy cabling.
Ring Topology
Ring Topology forms an unbroken circle of network nodes, with data flowing in one direction.
Features of Ring Topology:
- Direct Connection: Each node is directly connected to the ring.
- No Central Device: Does not require a central hub.
Limitations of Ring Topology:
- Single Point of Failure: Node failure affects the entire network.
- Troubleshooting: Difficult to identify problems.
Mesh Topology
Mesh Topology connects each node to multiple other nodes. Data is transmitted on the shortest path between nodes.
Features of Mesh Topology:
- Robustness: Very robust and reliable.
- No Single Point of Failure: No single point of failure.
Limitations of Mesh Topology:
- Complexity: Complex cabling and connectivity.
- Cost: High cost due to cabling.
Hybrid Topology
Features of Hybrid Topology:
- Flexibility: Highly flexible.
- Scalability: Scalable and adaptable to specific needs.
Limitations of Hybrid Topology:
- Complexity: Complicated configuration.
- Cost: Expensive to implement.
Open Systems Interconnection (OSI) Model
- Data Link Layer: Ensures reliable node-to-node data transfer by detecting and correcting errors. It manages MAC (Media Access Control) addresses and frame synchronization.
- Network Layer: Responsible for logical addressing and routing. It determines the best path for data transfer between devices across different networks using protocols like IP (Internet Protocol).
- Transport Layer: Ensures end-to-end communication and data integrity. It manages flow control, error correction, and segmentation of data using protocols like TCP (Transmission Control Protocol) and UDP (User Datagram Protocol).
- Session Layer: Manages sessions between applications. It establishes, maintains, and terminates communication sessions between devices, ensuring proper data exchange.
- Presentation Layer: Translates data between the application layer and the network. It handles data encryption, compression, and formatting to ensure compatibility between different systems.
- Application Layer: Provides network services directly to user applications. It supports protocols like HTTP, FTP, SMTP, and DNS, enabling applications to access network resources.
Transmission Media
Transmission media are the “roads” that allow information to move between devices, like between your computer and the internet.
Transmission Media refers to the physical pathways used to transmit data between devices in a network. It can be classified into two main types: guided and unguided media.
Guided Media (wire)
Guided media involves physical cables that guide data signals along a specific path.
Types of Guided Media:
- Twisted Pair Cable:
- Unshielded Twisted Pair (UTP): Commonly used in telephones and computer networks, it consists of pairs of wires twisted together to reduce electromagnetic interference.
- Shielded Twisted Pair (STP): Similar to UTP but with an additional shielding layer to provide better protection against interference.
- Coaxial Cable: Consists of a central conductor, an insulating layer, a metallic shield, and an outer protective layer. It is used for cable TV and broadband internet connections.
- Fiber Optic Cable: Transmits data as light signals through thin strands of glass or plastic fibers. It offers high-speed data transmission and resistance to electromagnetic interference, making it ideal for long-distance communication.
Unguided Media (wireless)
Unguided media uses wireless signals to transmit data through the air without physical cables.
Types of Unguided Media:
- Radio Waves: Used for wireless communication over long distances, such as AM/FM radio, television broadcasting, and mobile phones.
- Microwaves: Used for point-to-point communication over short and long distances, including satellite communications and wireless LANs.
- Infrared: Used for short-range communication between devices like remote controls and computer peripherals.
Comparison of Twisted Pair, Coaxial, Fiber Optic, and Unguided Media
| Type | Description | Use Cases |
|---|---|---|
| Unshielded Twisted Pair (UTP) | Commonly used in telephones and computer networks, UTP consists of pairs of wires twisted together to reduce electromagnetic interference. | Telephones, Ethernet networks. |
| Shielded Twisted Pair (STP) | Similar to UTP but with an additional shielding layer to provide better protection against interference. | Environments with higher electromagnetic interference, such as industrial settings. |
| Coaxial Cable | Consists of a central conductor, an insulating layer, a metallic shield, and an outer protective layer. | Cable TV, broadband internet connections. |
| Fiber Optic Cable | Transmits data as light signals through thin strands of glass or plastic fibers. | High-speed data transmission, long-distance communication, internet backbone. |
| Radio Waves | Used for wireless communication over long distances. | AM/FM radio, television broadcasting, mobile phones. |
| Microwaves | Used for point-to-point communication over short and long distances. | Satellite communications, wireless LANs. |
| Infrared | Used for short-range communication between devices. | Remote controls, computer peripherals. |
Network Protocols
Network Protocols are sets of rules and conventions that govern data communication between devices in a network. They ensure reliable data transmission, addressing, error handling, and more.
Common Network Protocols
- HTTP (Hypertext Transfer Protocol): The foundation of data communication on the World Wide Web, used for transmitting web pages and other resources.
- HTTPS (Hypertext Transfer Protocol Secure): An extension of HTTP with added security for encrypting data between the browser and the server using SSL/TLS.
- FTP (File Transfer Protocol): Used for transferring files between computers on a network, supporting file upload and download.
- SMTP (Simple Mail Transfer Protocol): Used for sending and receiving email messages between mail servers.
- POP3 (Post Office Protocol 3): Retrieves emails from a mail server to a local client, downloading messages for offline access.
- IMAP (Internet Message Access Protocol): Allows users to access and manage their email on the server, enabling synchronization across multiple devices.
- DNS (Domain Name System): Translates domain names into IP addresses, allowing users to access websites using easy-to-remember names instead of numerical IP addresses.
- TCP (Transmission Control Protocol): Provides reliable, ordered, and error-checked data transmission between applications over a network.
- UDP (User Datagram Protocol): Offers a simpler, connectionless communication model with no error recovery, suitable for applications that require fast transmission, such as video streaming and gaming.
- IP (Internet Protocol): Responsible for addressing and routing data packets between devices on different networks.
Network Security
Network Security involves protecting network infrastructure, data, and devices from unauthorized access, attacks, and damage. It encompasses various technologies, processes, and practices to safeguard information and ensure data integrity.
Key Aspects of Network Security
- Authentication: Verifying the identity of users and devices accessing the network. Common methods include passwords, biometrics, and two-factor authentication (2FA).
- Encryption: Converting data into a secure format to prevent unauthorized access. Encryption algorithms like AES (Advanced Encryption Standard) and RSA (Rivest-Shamir-Adleman) are widely used for securing data transmission.
- Firewall: A network security device that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Firewalls help protect networks from unauthorized access and cyber threats.
- Intrusion Detection and Prevention Systems (IDPS): Monitor network traffic for suspicious activities and take action to prevent potential security breaches.
- Virtual Private Network (VPN): Provides secure remote access to a network over the internet, encrypting data and ensuring privacy for users.
- Access Control: Restricting access to network resources based on user roles and permissions, ensuring that only authorized users can access sensitive information.
- Antivirus and Anti-malware Software: Protects devices and networks from malicious software, including viruses, worms, and ransomware, by detecting and removing threats.
- Security Policies: Establishing guidelines and procedures for network security management, including user behavior, data handling, and incident response.
Common Network Security Threats
- Malware: Malicious software designed to damage or disrupt systems, including viruses, worms, Trojan horses, and spyware.
- Phishing: A form of social engineering where attackers deceive users into revealing sensitive information, such as login credentials or financial data, by posing as a trustworthy entity.
- Denial of Service (DoS) Attack: An attempt to make a network resource unavailable by overwhelming it with traffic, disrupting normal service.
- Man-in-the-Middle Attack: Intercepting and altering communication between two parties without their knowledge, potentially leading to data theft or manipulation.
- SQL Injection: Exploiting vulnerabilities in a web application's database query execution, allowing attackers to execute malicious SQL code and access sensitive data.
- Zero-Day Exploit: Attacks targeting software vulnerabilities unknown to developers, leaving systems exposed until patches are released.
Cloud Computing
Cloud Computing refers to delivering computing resources and services, such as servers, storage, databases, networking, and software, over the internet (the cloud). It enables organizations and individuals to access and use these resources on-demand, without the need to own or manage physical infrastructure.
Key Characteristics of Cloud Computing
- On-Demand Self-Service: Users can access computing resources and services whenever needed without requiring human intervention from the service provider.
- Broad Network Access: Resources and services are accessible over the internet, supporting a wide range of devices, including desktops, laptops, smartphones, and tablets.
- Resource Pooling: Cloud providers pool their computing resources to serve multiple users simultaneously, optimizing resource utilization and cost-efficiency.
- Rapid Elasticity: Resources can be quickly scaled up or down based on user demand, allowing for flexibility and responsiveness to changing needs.
- Measured Service: Cloud services are monitored and billed based on usage, enabling cost transparency and efficient resource management.
Types of Cloud Computing Services
- Infrastructure as a Service (IaaS): Provides virtualized computing resources over the internet, including virtual machines, storage, and networking. Users can manage and control the underlying infrastructure.
Examples: Amazon EC2, Google Compute Engine, Microsoft Azure Virtual Machines.
- Platform as a Service (PaaS): Provides a platform for developing, testing, and deploying applications without managing the underlying infrastructure. Users can focus on application development and deployment.
Examples: Google App Engine, Microsoft Azure App Service, Heroku.
- Software as a Service (SaaS): Delivers software applications over the internet, accessible through web browsers or client applications. Users do not need to install or manage the software on their devices.
Examples: Google Workspace, Microsoft Office 365, Salesforce, Zoom.
Deployment Models of Cloud Computing
- Public Cloud: Cloud infrastructure is owned and operated by a third-party service provider and made available to the general public. Public clouds offer cost-effective solutions and are ideal for businesses with variable workloads.
- Private Cloud: Cloud infrastructure is dedicated to a single organization, providing more control and security. It is suitable for businesses with specific regulatory or security requirements.
- Hybrid Cloud: Combines public and private clouds, allowing data and applications to be shared between them. It offers greater flexibility and scalability while maintaining security and compliance.
- Community Cloud: Shared infrastructure for specific communities with common concerns, such as industry regulations or security requirements. It is managed by one or more organizations or a third-party provider.
Benefits of Cloud Computing
- Cost Savings: Reduces the need for physical infrastructure and maintenance, leading to lower IT costs.
- Scalability: Provides the ability to scale resources up or down based on demand, ensuring optimal performance.
- Flexibility: Enables access to resources and services from anywhere with an internet connection, supporting remote work and collaboration.
- Disaster Recovery: Offers data backup and recovery solutions, ensuring business continuity during disasters or outages.
- Automatic Updates: Ensures that software and infrastructure are updated with the latest features and security patches.
Challenges of Cloud Computing
- Security and Privacy: Concerns about data protection, privacy, and compliance with regulations in shared environments.
- Downtime and Reliability: Potential for service outages or disruptions affecting business operations.
- Vendor Lock-In: Dependence on a specific cloud provider's infrastructure and services, making it challenging to switch providers.
- Data Transfer and Latency: Concerns about data transfer speeds and latency for applications requiring real-time processing.
Internet of Things (IoT) (continued)
Key Components of IoT
- Devices and Sensors: Physical objects equipped with sensors and actuators collect data from the environment and interact with other devices.
- Connectivity: Communication protocols and networks enable devices to connect and share data, including Wi-Fi, Bluetooth, cellular networks, and LoRaWAN.
- Data Processing and Analysis: Data collected by devices is processed and analyzed to derive meaningful insights, often using cloud-based platforms and analytics tools.
- User Interface: Applications and dashboards allow users to interact with and control IoT devices, providing real-time information and control.
Applications of IoT
- Smart Home: IoT devices enhance home automation and energy management, including smart thermostats, lighting, and security systems.
- Healthcare: Wearable devices and remote monitoring systems track patient health, enabling personalized care and early intervention.
- Industrial IoT (IIoT): IoT technologies optimize manufacturing processes, predictive maintenance, and supply chain management.
- Agriculture: IoT sensors monitor soil conditions, weather, and crop health, improving precision farming and resource management.
- Transportation and Logistics: IoT solutions improve vehicle tracking, fleet management, and supply chain efficiency.
- Smart Cities: IoT infrastructure enhances urban living through intelligent traffic management, waste management, and energy efficiency.
Benefits of IoT
- Efficiency and Automation: IoT automates processes, reducing manual intervention and increasing efficiency.
- Data-Driven Decision Making: Real-time data collection and analysis enable informed decision-making and optimization.
- Improved Quality of Life: IoT applications enhance convenience, safety, and comfort in various aspects of daily life.
- Cost Savings: IoT solutions optimize resource usage, reducing operational costs and improving productivity.
Challenges of IoT
- Security and Privacy: Concerns about data security, unauthorized access, and privacy in connected environments.
- Interoperability: Ensuring compatibility and communication between diverse devices and platforms.
- Data Management: Handling large volumes of data generated by IoT devices requires robust storage and processing capabilities.
- Scalability: Managing and scaling IoT networks as the number of connected devices grows.
Conclusion
Understanding the fundamentals of data communication and networking is essential in today's interconnected world. From the OSI model and network topologies to cloud computing and the Internet of Things, these technologies shape how we communicate, work, and live. By leveraging the power of networks, we can achieve greater efficiency, security, and innovation across various industries and applications.
As technology continues to evolve, the field of data communication will undoubtedly see new advancements and challenges. Staying informed about these developments is crucial for professionals in IT, telecommunications, and related fields. The concepts covered in this overview provide a solid foundation for understanding current technologies and preparing for future innovations in data communication and networking.